Drama is great, on so many levels. When HBO released the series
Sillicon Valley, I loved it - it made fun of something that I felt so
connected to. Now Ubisoft has released a game called Watch Dogs 2, which
makes me evoke none of the same emotions, despite my love of infosec.
(Ubisoft hasn't bribed me sent me a review copy yet, so I can say whatever I want)
But with LG recently announcing that every new fridge, washing machine and dishwasher will ship with wifi this year, I got a little worried. Sure, there has been so much talk of "Internet of Things" and "Smart Cities", but it always felt so far away.
Then I went through the list of hacks in the game, and OH MY GOD. I found that White Hats have already found ways to do all but one of the hacks in Ubisoft's fictional creation. The 15 hacks are as follows:
City Disruption
1 - Traffic Control Exploit - Hack the traffic light system to create accidents and stop pursuers.
In 2014, University of Michigan researched analysed the security of traffic light systems that are deployed in the USA. In Michigan, different sets of lights would wirelessly connect to a central server to better co-ordinate the traffic flow. The network was 5.8GHz, showed up in the Wi-Fi listing and was completely unencrypted. The only reason that it took longer to hack it was the propriety network protocol. Too easy!
2 - System Crash Upgrade: Blackout - Turns off all lights in area.
Consumer light bulbs are toast at this point. Black Hat 2016 didn't have any hacking to turn the lights on and off. No, Black Hat 2016 featured making a botnet of lightbulbs. Because why not, right?
But aren't city street lights just dumb and timer based? Hell no! It is 2017
- time for "smart cities" and "connected data backbones". That's what many, vendors seem to think. I'm pretty hyped that my home city of Canberra is getting smart street lights soon. Maybe installing so many security nightmares will put Canberra on the infosec conference map?

3 - Security System Shutdown - Shut down security systems.
Hacking home alarm systems is soo 2014!. And security cameras have been done to death. Given the number of cameras wide open on the internet, wouldn't this be fun?
4 - Massive System Crash - Shut down all city infrastructure for 30 seconds.
Power grids are pretty high-value targets, and probably have the ability to mess with a huge chunk of city infrastructure. This topic has been hacked time and time again. From the glamour of Stuxnet, to frequent scares with varying levels of importance. Power grids are full of computers driving complex markets and machines - many of them vulnerable.
5 - Auto-Takedown - Trigger Gates and Steam Pipes when enemy vehicles pass nearby.
Many "smart" locks can be easily hacked. See this BlackHat 2016 talk about bluetooth smart locks, or this attack brute-forcing garage door lock's 12 bit keys in 8 seconds.

As for the steam pipes, I don't think that San Francisco has steam pipes conveniently placed under roads. Even if there were steam pipes, it might be possible to "hack" them using a sledge hammer!
6 - Robot Exploits - Create a Distraction on robots.
Hacking a professional drone - Nils Rodday - RSA Conference 2016.
Vehicle Hacking
7 - Vehicle Directional Hack - Hack vehicles to move in specific directions.
8 - Engine Override - Trigger a burst of speed in a vehicle.
9 - Massive Vehicle Hack - When on-foot, create mayhem by hacking all cars in the area at once. While driving, hack vehicles to distract drivers and clear a path.

In 2015, Charlie Miller & Chris Valasek uncovered some pretty legendary vulnerabilities in the Jeep line of cars. They were able to demonstrate how a unaltered car could be remotely exploited, then they could move laterally and send CAN Bus messages to steer the car. Hundreds of kilometers away, the car would be remote controlled.
They also released a paper in 2014, looking at the architecture of electronic systems in a huge range of cars. Reading about plane hacking is intersting, because areoplanes include strict systems to separate the cabin from the cockpit. The car's electronic systems are built to nowhere near the standards of an aeroplane - many cars have systems that communicate with the outside world connected to the CAN Bus. There is no concept of "security domains" or the like.
I think that the "Vehicle Directional Hack" is possibly one of the most accurate hacks in this game.
10 - Hijacker - Hack cars' electronic locks instead of lockpicking.
Car keys seem like a great time to apply public key cryptography. You have physical keys and cars - do you don't have to deal with key transfer across the internet. Then it is simple - car issues a challenge, key signs the challenge, car validates the signature.
Unfortunately running crypto computations on something like a key is hard - keys don't have a lot of power! Also, car manufacture's don't have a great track record for security.
This has turned into a bit of a "cat and mouse game". Most recently, Flavio D. Garcia, et. al. released a paper finding that:
- VW group cars share 4 global master crypto keys
- the common Hitag2 scheme (used by Fiats, Fords and others) can be broken in less than 10 minutes.
Nice.
Remote Control
11 - Environmental RC - Remote control for forklifts, scissor lifts, and cranes.
You can't make a fictional video game without some fiction. I actually haven't seen anybody do this yet! Good job?!
12 - Proximity Scanner - Equip the Quadcopter with enhanced Scanning capacity. NPCs are tagged through walls while controlling the Quadcopter in NetHack.
Phones, tablets and smartwatches are all tracking us as we speak. That makes anybody's Google or iCloud account quite a high value target. Whether it is a telephone company defeating your google account's 2fa or Apple support's helpful account recovery, these are targets that have been hacked.
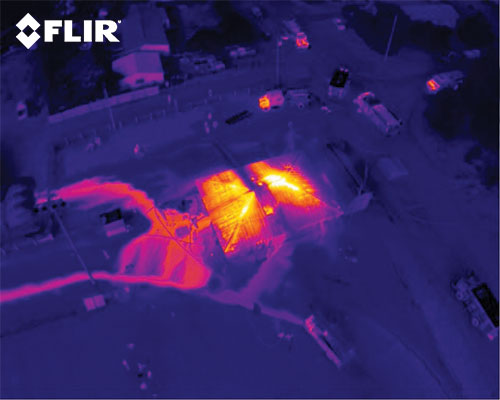
But if you're going to get your hands dirty with a drone, why not just use a thermal camera on a drone? According to my trustworthy video-games experience, thermal camera very reliable for finding hiding enemies.
Social Engineering
13 - Create Distraction - This hack sends a distraction to civilian phones or blasts feedback in enemy headsets. It also cancels 911 and reinforcement calls.
This one isn't a hack. It is simple - a magical, courageous feature by Apple called iBeacon. It even notifies you if your phone is locked!
14 - APB: Suspect Located - Place a false APB on your target and broadcast the location. The police will come to arrest the target.
15 - APB: Wanted Criminal - Place a false APB on your target with a special "dangerous criminal" advisory.

Maybe Brain Krebs would have an opinion on this topic? He has a whole category on swatting on his blog, which is when attackers manage to get a SWAT team dispatched to the victims house. He has even been the victim of swatting himself.
Conclusion
The developers behind Watch Dogs 2 seem to have created a pretty broad range of 15 hacks across a variety of different systems. What's even more amazing to me is that only 1 of them is fictional.
But what does this say about the state of "Smart City" and IoT security? This makes me very, very worried.
I hope you enjoyed this article. Contact me if you have any thoughts or questions.
© 2015—2025 Sam Parkinson